SlotsPlus Casino
SlotsPlus Casino is an award winning online casino, known for being a great place to gamble online. Since 2002, SlotsPlus Casino has been offering players some of the best slots and casino gaming online. SlotsPlus Casino is owned and operated by the Mainstreet Group, one of the more reputable online casino owners in the world today.
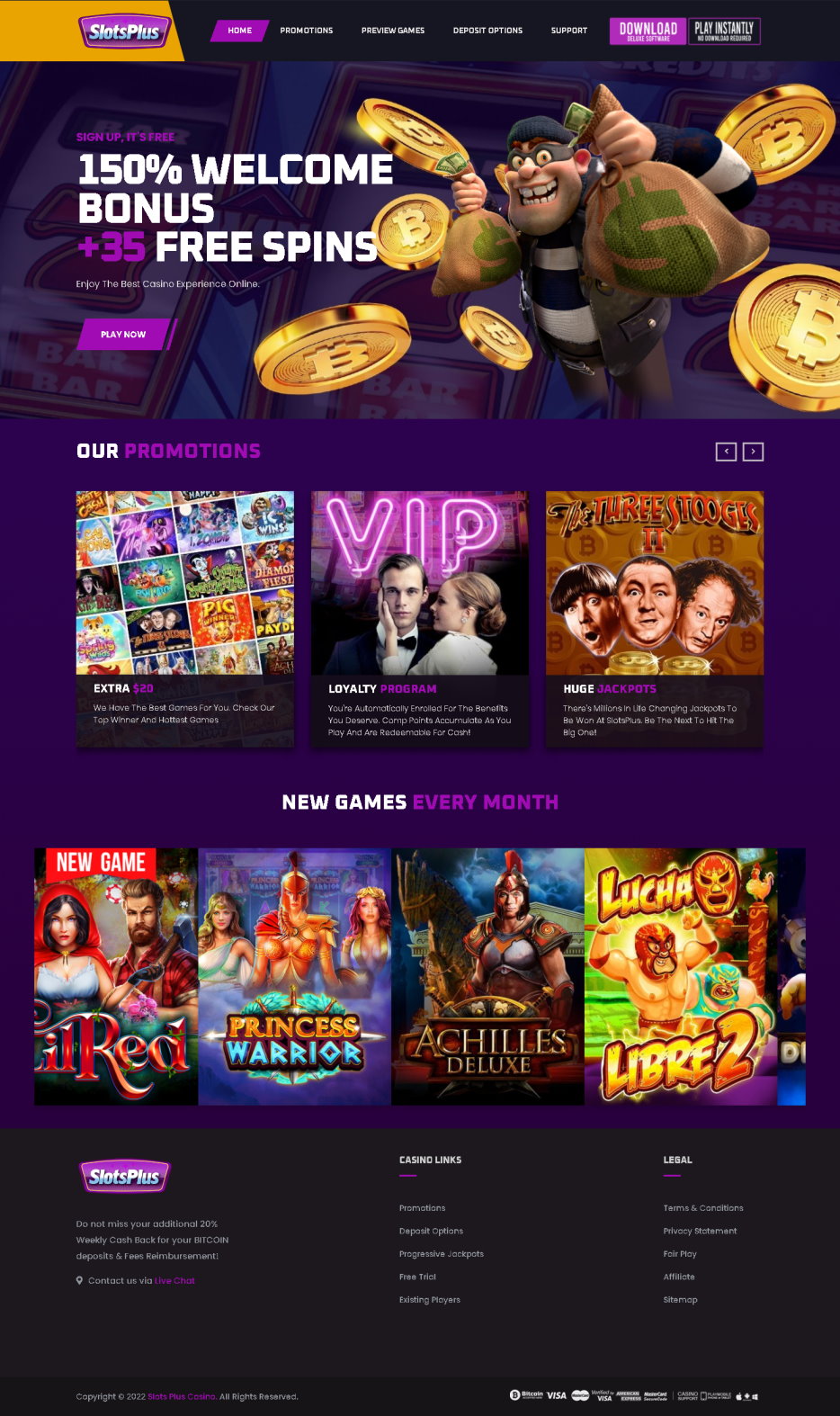
The free bonuses are really exciting at SlotsPlus Casino. You have the initial sign up bonus of $125 with 125% reward. Very satisfying! Then there is the high roller best bonus of $25000 with 25% rewards. This is cashable and can be redeemed before the game.
SlotsPlus Casino runs on software powered by Realtime Gaming. The software is one of the top developers of gaming software for the online gambling industry. You will find both downloadable software and a no download option for both Windows and Mac players. Players enjoy the easy to navigate software and great graphics, as well as the extensive choice of games and bonus options. Each title has colorful and vibrant graphics with excellent sound effects
SlotsPlus Casino understands the need for players to be able to enjoy their favorite games even when computer access to the site is not readily available. As a result, the casino has designed and released an exclusive mobile version of its allcasino site that can be played through almost any mobile device.
The cutting-edge online slots software, regular promotions including cash, vacation packages ad many more, make SlotsPlus Casino reward program one of the best loyalty casinos online. SlotsPlus Casino also offers live games and 24/7 support by chat, email or phone and the dealer voices and sharp 3D environments grant this online casino a unique personality.
SlotsPlus Casino offers over 200 games, more than fifty of which are slots. The casino offers card and table games, video slots, classic slots, progressive games video poker and keno. You will find both American style and European style roulette here and all the major card and table games, as well as some of the less known in American casinos, such as the classic baccarat and fast moving war.
With SlotsPlus Casino, you have a wide range of options to choose from when it comes to online banking and gambling. Major credit and debit cards are accepted, as are virtual wallets, prepaid cards, online banking and bank transfers. One of the popular payment methods is the POLi web wallet.
SlotsPlus Casino support can be reached via email, phone, or live chat. They have support 24 hours a day, 7 days a week. Also available is a toll free number. It is suggested that you use the live chat feature as this will give you the quickest response. Please only use the support features if your question has not been answered by the FAQ page.